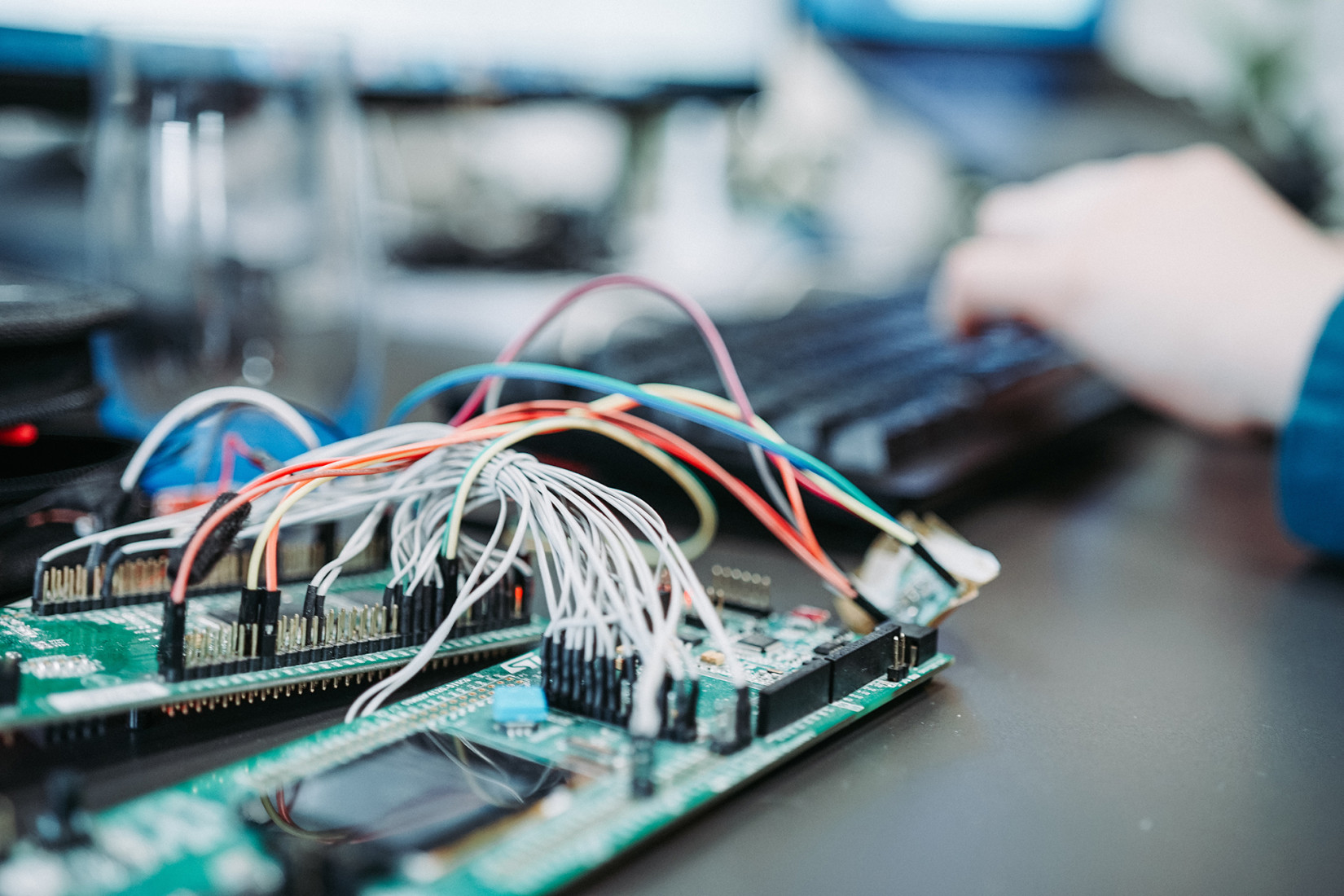
IoT technology continues to evolve at a rapid pace – and we are making sure we stay at the cutting edge of utilizing transformational technology. We recently arranged for two of our engineers to attend a three-day course with Microsoft in order to find out more about the latest developments on Azure Sphere.
More than 9 billion microcontrollers (MCU) are produced every year. These MCUs can be found in almost all electronic devices in your cars, offices and homes. However, less than 1% of MCUs are connected to the internet. That means these units are closed systems that cannot be integrated with broader networks. With network connectivity, many industries would be transformed – creating opportunities for new ways to connect with customers and monitor the performance of instruments.
Although internet-connected MCUs are not necessary in all electronics, we have spent time understanding which use cases network-integrated MCUs can provide the most value. While connecting these MCUs to broader networks or the worldwide web may sound trivial, it’s not all that straightforward...
There is an enormous risk associated in coupling hardware with the internet. There have been many cases in recent years of IoT units being compromised and misused. Fortunately, Microsoft’s Azure Sphere has made secure connectivity much easier.
Azure Sphere is an end-to-end solution to secure IoT units. It consists of three elements:
Azure Sphere Certified Chips
Azure Sphere OS
Azure Sphere Security Service
Together, the elements cover seven properties that are important for securing the units. These properties cover both software and hardware. This article from Microsoft provides a more detailed description – Seven Properties of Highly Secure Devices.
Azure Sphere Certified Chips are MCUs that align with Microsoft’s security protocols and hardware guidelines. These are available from a number of different manufacturers. The purpose of the certification is to establish a hardware layer that can be trusted. Each chip is assigned a unique ID when it is produced. In fact, the whole Azure Sphere solution utilizes certificate-based security. A private key is concealed in the unit. When combined with the official key, it functions as its unique ID.
To ensure that the unit cannot be manipulated, even when someone may have physical access to it, the unit must be ‘finalized’ at the end of the process. This means that it can only be reprogrammed by means of updates retrieved from the Azure Sphere Security Service. Every time the unit starts up, it will ping the application and retrieve any updates from the cloud. Azure Sphere OS is based on a purpose-built Linux core with a layered model for security. Applications run separately with different cores for different purposes: Low-level to IO and general purpose to high-level computing. A SDK (Software Development Kit) is used to ensure secure communication between them. Updating mechanisms are built in for both the operating system itself and for applications.
In the event of any security gaps, it is possible to address these by using the Windows Update infrastructure. Applications can indicate whether they want to wait for updates, preventing units from restarting at an inconvenient time. In the event of restart, it only takes a few seconds to make an update. This means downtime is limited.
Backward compatibility is given top priority. Developers do not need to worry about a new OS update destroying the application. The application treats this as essential property, ensuring that customers’ products will not suddenly stop working.